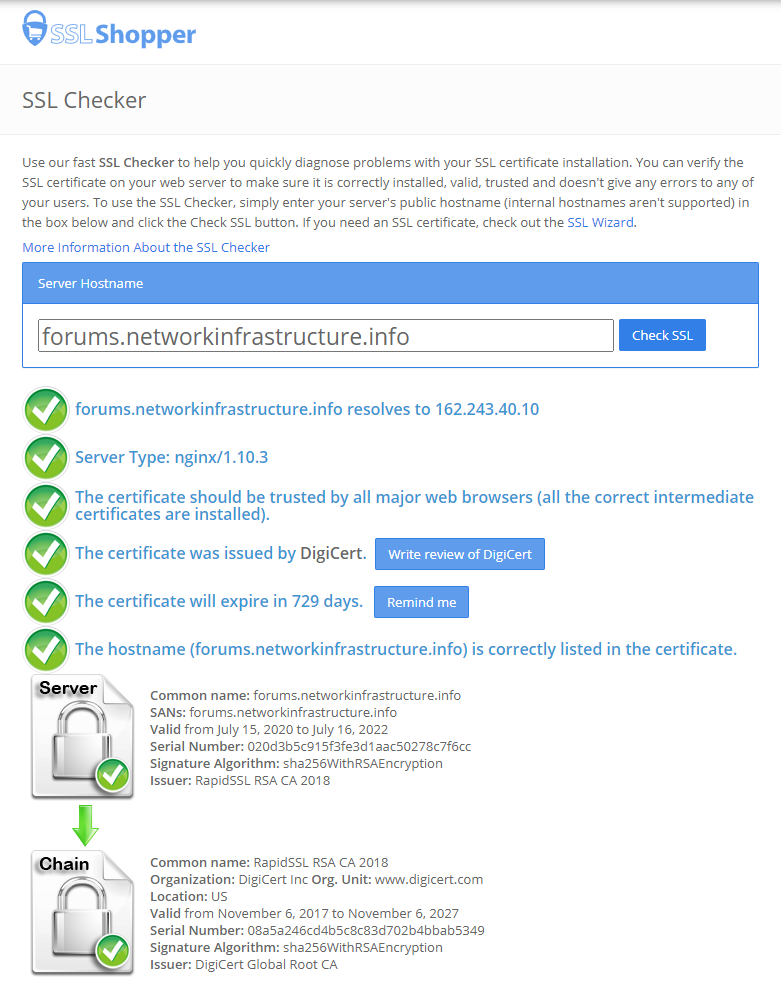
It’s been over a year since I posted here but I finally found the time to migrate away from GoDaddy. And I will once again be able to fully automate renewing my wildcard SSL certificates with LetsEncrypt while saving some $$$ as well.
This has been a long time coming… and while I didn’t have any really bad experiences with GoDaddy I’ve likely been leaving a good chunk of change on the table every year with the costs I’ve been paying for the few domains that I actually own.
I’ve also starting looking at OVHcloud, possible migrating away from Digital Ocean. Who knows maybe by the time you are reading this, this site will already have been migrated.
Cheers!