It turns out that in the year 2022 upgrading from PAN-OS 8.0.x requires a TAC case and an older content update file that’s not readily available on Palo Alto’s Support website.. Hopefully this will save someone else the down the road.
I recently needed to press an older PA-220 that had been in laying around in a lab into a production environment due to the supply chain debacle that we’re all currently living in. I reached out to my reseller and had the firewall fully licensed and was able to apply those licenses to the hardware. In preparation of the deployment I tried to bring the PA-220 up to PAN-OS 9.1.14. And was unable to upgrade past 8.0.20 even with the device being fully licensed.
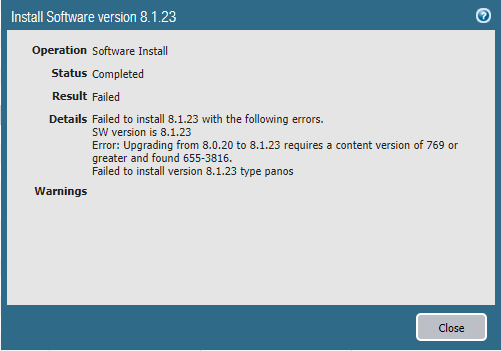
When I tried to upgrade from 8.0.20 to 8.1.23 I would get an error during the software install, “Failed to install 8.1.23 with the following errors. SW version is 8.1.23 Error: Upgrading from 8.0.20 to 8.1.23 requires a content version of 769 of greater and found 655-3816. Failed to install version 8.1.23 type panos“
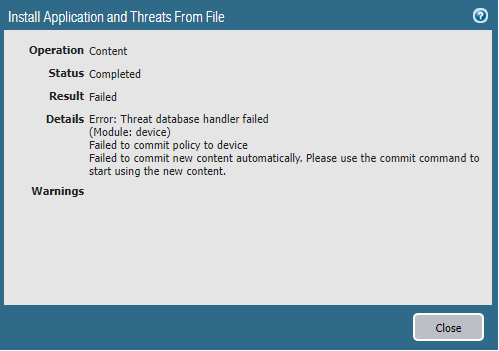
Even though the device was fully licensed there were no Dynamic Updates available to download or install. I even tried to manually download them from the Palo Alto support website and install them and that was met with a different error when trying to commit the change.
I opened a case with Palo Alto Support and eventually they provided me content update 8424-6791 which I was able to manually install and apply, after which I was successfully able to upgrade to 8.1.23. I was then able to download and apply the latest and greatest greatest content updates from the webUI and eventually upgrade the firewall to 9.1.14.
Cheers!