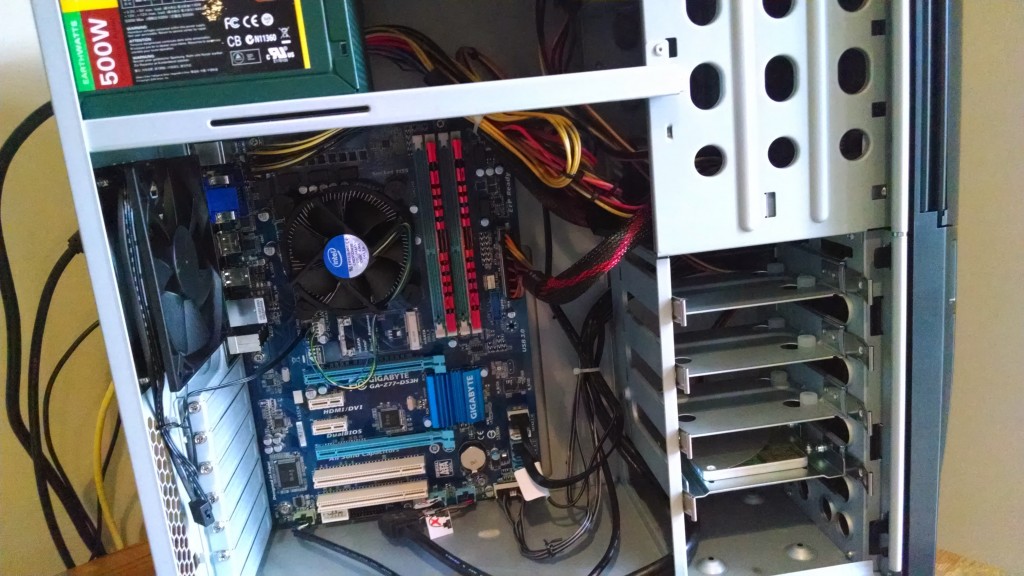
In November I got a call from my parents that the desktop I built for them back in 2014 was not booting up. After talking my father through opening the case and sending me some video, it appeared that the case and CPU fans would start but then stop, only to start again and then stop again, rinse and repeat over and over. I had seen this symptom before and thought the issue might be with the power supply so I ordered a new EVGA 500W power supply and had it shipped to their house. Kudos to my 70 year old father for replacing the power supply by himself, unfortunately the problem persisted so that likely meant that the motherboard had failed, although the motherboard looked fine and there were no obvious failed capacitors or other damage.
That machine had lasted them six years, so that was a pretty good investment in my honest opinion and I could likely reuse the case, power supply, CPU and memory from that computer on other builds or projects my daughters were working on. In the end I decided to just build them a new machine, swapping the SSD from their old machine, this way there would be minimal change to them. All their email and shortcuts would be there, all the software would be the same, the icons would all be in the “right” place. It would just make things super simple for them as the user, especially since both of my parents are in their 70s.
I went and ordered a bunch of new components to build them a new machine.
- GIGABYTE H370M DS3H (LGA1151/Intel/H270/USB 3.1 Gen 1 (USB3.0) Type A Type C/Micro ATX/DDR4/Motherboard)
- Corsair Vengeance LPX 16GB (2x8GB) DDR4 DRAM 3000MHz C15 Desktop Memory Kit – Black (CMK16GX4M2B3000C15)
- Intel Core i5-9400 Desktop Processor 6 Cores 2. 90 GHz up to 4. 10 GHz Turbo LGA1151 300 Series 65W Processors BX80684I59400
- Thermaltake UX100 5V Motherboard ARGB Sync 16.8 Million Colors 15 Addressable LED Intel/AMD Universal Socket Hydraulic Bearing 65W CPU Cooler CL-P064-AL12SW-A
- Thermaltake Versa H18 Tempered Glass Black Spcc Micro ATX Gaming Computer Case CA-1J4-00S1WN-01
- Thermaltake Smart 500W 80+ White Certified PSU, Continuous Power with 120mm Ultra Quiet Cooling Fan, ATX 12V V2.3/EPS 12V Active PFC Power Supply PS-SPD-0500NPCWUS-W
- Windows 10 Home 32-bit/64-bit – OEM – (Product Key Code Email Delivery)
With the help of my youngest daughter we assembled the the pieces of the new machine and then tested that everything was working properly using a spare SSD that I had available.
My parents brought the old machine over to my house, I removed the SSD and installed it into the new machine, cleaned up some of the drivers, installed a new Windows 10 license key (OEM version would not re-activate) and they were back up and running with minimal fuss to them.
Let’s see how long that machine lasts them.
Cheers!